File:CIAJMK1209-en.svg
From Wikipedia, the free encyclopedia

Size of this PNG preview of this SVG file: 496 × 496 pixels. Other resolutions: 240 × 240 pixels | 480 × 480 pixels | 768 × 768 pixels | 1,024 × 1,024 pixels | 2,048 × 2,048 pixels.
Original file (SVG file, nominally 496 × 496 pixels, file size: 177 KB)
| This is a file from the Wikimedia Commons. Information from its description page there is shown below. Commons is a freely licensed media file repository. You can help. |
Summary
| DescriptionCIAJMK1209-en.svg |
العربية: طبقات أمن المعلومات حسب وكالة الاستخبارات المركزية، الإصدار الثاني
English: Information Security, CIA triad. Confidentiality, Integrity, Availability. Second version |
|||||||||||||||||
| Date | ||||||||||||||||||
| Source |
This file was derived from: CIAJMK1209.png |
|||||||||||||||||
| Author |
creator QS:P170,Q81411358 |
|||||||||||||||||
| Other versions |
|
|||||||||||||||||
Licensing
I, the copyright holder of this work, hereby publish it under the following license:
This file is licensed under the Creative Commons Attribution-Share Alike 4.0 International license.
- You are free:
- to share – to copy, distribute and transmit the work
- to remix – to adapt the work
- Under the following conditions:
- attribution – You must give appropriate credit, provide a link to the license, and indicate if changes were made. You may do so in any reasonable manner, but not in any way that suggests the licensor endorses you or your use.
- share alike – If you remix, transform, or build upon the material, you must distribute your contributions under the same or compatible license as the original.
Captions
https://en.wikipedia.org/wiki/Software/m.tolte.company/
سیکل امنیت داده
데이터 보안주기
Veri güvenliği döngüsü
การยืนยันแบบสองขั้นตอน
Items portrayed in this file
depicts
5 February 2022
image/svg+xml
f643256456e21484ffc78fdef715a08e76ff1170
181,529 byte
496 pixel
496 pixel
File history
Click on a date/time to view the file as it appeared at that time.
| Date/Time | Thumbnail | Dimensions | User | Comment | |
|---|---|---|---|---|---|
| current | 01:46, 22 April 2023 |  | 496 × 496 (177 KB) | Hohum | centered elements |
| 14:12, 1 October 2022 | 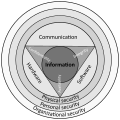 | 496 × 496 (178 KB) | Hohum | Straighten text, make CIA element more prominent | |
| 09:34, 5 February 2022 |  | 496 × 496 (177 KB) | Michel Bakni | Uploaded own work with UploadWizard |
File usage
More than 100 pages use this file. The following list shows the first 100 pages that use this file only. A full list is available.
- Advanced persistent threat
- Adware
- Anomaly detection
- Antivirus software
- Application firewall
- Application security
- Arbitrary code execution
- Authentication
- Authorization
- Backdoor (computing)
- Botnet
- Brewer and Nash model
- Browser Helper Object
- Code injection
- Computer access control
- Computer fraud
- Computer security
- Computer security software
- Computer virus
- Computer worm
- Copy protection
- Crimeware
- Cross-site scripting
- Cyberattack
- Cybercrime
- Cybergeddon
- Cyberstrategy 3.0
- Cyberterrorism
- Cyberwarfare
- Data breach
- Data masking
- Denial-of-service attack
- Dialer
- Digital privacy
- Digital rights management
- Drive-by download
- EICAR test file
- Eavesdropping
- Electromagnetic warfare
- Email fraud
- Email spoofing
- Encryption
- Exploit (computer security)
- Firewall (computing)
- Fork bomb
- Fuzzing
- Hacktivism
- Hardware Trojan
- Host-based intrusion detection system
- Information security
- Information security standards
- Information warfare
- Internet security
- Intrusion detection system
- Keystroke logging
- Logic bomb
- Malware
- Microsoft Security Development Lifecycle
- Misuse case
- Mobile secure gateway
- Mobile security
- Multi-factor authentication
- Network security
- Obfuscation (software)
- Payload (computing)
- Phishing
- Polymorphic engine
- Privilege escalation
- Ransomware
- Remote desktop software
- Rogue security software
- Rootkit
- SQL injection
- Scareware
- Secure by default
- Secure by design
- Secure coding
- Security-focused operating system
- Security bug
- Security hacker
- Security information and event management
- Security testing
- Shellcode
- Social engineering (security)
- Software bug
- Software security assurance
- Spamming
- Spyware
- Stateful firewall
- Threat (computer)
- Time bomb (software)
- Trojan horse (computing)
- Voice phishing
- Vulnerability (computing)
- Vulnerability management
- Vulnerability scanner
- Web application firewall
- Wiper (malware)
- Zip bomb
- Zombie (computing)
View more links to this file.
Global file usage
The following other wikis use this file:
- Usage on ar.wikipedia.org
- Usage on az.wikipedia.org
- Avtorizasiya
- İnformasiya təhlükəsizliyi
- Autentifikasiya
- Kibertəhlükəsizlik
- İnformasiya təhlükəsizliyi və hadisə idarəetməsi
- Casus proqram
- Eksployt
- Boşluq (informatika)
- Kibermüharibə
- Kibercinayət
- Şablon:İnformasiya təhlükəsizliyi
- EICAR test faylı
- İmtiyazların artırılması
- SQL inyeksiyası
- Çoxfaktorlu autentifikasiya
- Arxa qapı
- Usage on bn.wikipedia.org
- ফায়ারওয়াল (কম্পিউটিং)
- অ্যান্টিভাইরাস সফটওয়্যার
- কম্পিউটার ভাইরাস
- ডিনাইয়াল অব সার্ভিস
- ফিশিং
- কম্পিউটার নিরাপত্তা
- কম্পিউটার ওয়ার্ম
- র্যানসমওয়্যার
- সাইবার অপরাধ
- স্প্যামিং
- আক্রান্তপ্রবণতা (কম্পিউটিং)
- সাইবার সন্ত্রাসবাদ
- ম্যালওয়্যার
- গুপ্তায়ন
- সোশ্যাল ইঞ্জিনিয়ারিং (নিরাপত্তা)
- এসকিউএল ইনজেকশন
- কীস্ট্রোক লগিং
- সফটওয়্যার বাগ
- টেমপ্লেট:তথ্য নিরাপত্তা
- ব্যাকডোর (কম্পিউটিং)
- প্রমাণীকরণ
- তথ্য নিরাপত্তা
- পেলোড (কম্পিউটিং)
- সাইবারসেক্স পাচার
- অ্যাপ্লিকেশন নিরাপত্তা
- ২০২৩ সালের সর্বশেষ র্যানসমওয়্যার পরিসংখ্যান
- বহু-ধাপের প্রমাণীকরণ
- খসড়া:স্ক্রিপ্ট কিডি
- খসড়া:গ্রে হ্যাট (হ্যাকার)
- খসড়া:সাদা টুপি (কম্পিউটার নিরাপত্তা)
- খসড়া:কালো টুপি (কম্পিউটার নিরাপত্তা)
- Usage on ckb.wikipedia.org
View more global usage of this file.
Metadata
This file contains additional information, probably added from the digital camera or scanner used to create or digitize it.
If the file has been modified from its original state, some details may not fully reflect the modified file.
| Width | 496.16171 |
|---|---|
| Height | 496.16171 |
Retrieved from "https://en.wikipedia.org/wiki/File:CIAJMK1209-en.svg"

