Top Qs
Timeline
Chat
Perspective
Great Firewall
Chinese internet regulations From Wikipedia, the free encyclopedia
Remove ads
The Great Firewall (GFW; simplified Chinese: 防火长城; traditional Chinese: 防火長城; pinyin: Fánghuǒ Chángchéng) is the combination of legislative actions and technologies enforced by the People's Republic of China to regulate the Internet domestically.[1] Its role in internet censorship in China is to block access to selected foreign websites and to slow down cross-border internet traffic.[2] The Great Firewall operates by checking transmission control protocol (TCP) packets for keywords or sensitive words. If the keywords or sensitive words appear in the TCP packets, access will be closed. If one link is closed, more links from the same machine will be blocked by the Great Firewall.[3] The effect includes: limiting access to foreign information sources, blocking popular foreign websites (e.g. Google Search,[4] Facebook,[5] Twitter,[6] Wikipedia,[7][8] and others) and mobile apps, and requiring foreign companies to adapt to domestic regulations.[9][10]
Besides censorship, the Great Firewall has also influenced the development of China's internal internet economy by giving preference to domestic companies[11] and reducing the effectiveness of products from foreign internet companies.[12] The techniques deployed by the Chinese government to maintain control of the Great Firewall can include modifying search results for terms, such as they did following Ai Weiwei’s arrest, and petitioning global conglomerates to remove content, as happened when they petitioned Apple to remove the Quartz business news publication’s app from its Chinese App Store after reporting on the 2019–2020 Hong Kong protests.[13][14]
The Great Firewall was formerly operated by the SIIO, as part of the Golden Shield Project. Since 2013, the firewall is technically operated by the Cyberspace Administration of China (CAC), which is the entity in charge of translating the Chinese Communist Party's ideology and policy into technical specifications.
As mentioned in the "one country, two systems" principle, China's special administrative regions (SARs)—Hong Kong and Macau—are not affected by the firewall, as SARs have their own governmental and legal systems and therefore enjoy a higher degree of autonomy. Nevertheless, the U.S. State Department has reported that the central government authorities have closely monitored Internet use in these regions,[15] and Hong Kong's National Security Law has been used to block websites documenting anti-government protests.[16]
Provincial governments in parts of China, such as Henan Province, run their own versions of the firewall.[17][18][19]
The term Great Firewall of China is a combination of the word firewall with the Great Wall of China. The phrase "Great Firewall of China" was first used in print by Australian sinologist Geremie Barmé in 1997.[20][21]
Remove ads
History
Summarize
Perspective
A favorite saying of Deng Xiaoping's in the early 1980s, "If you open the window, both fresh air and flies will be blown in", is considered to be the political and ideological basis of the GFW Project.[nb 1] The saying is related to a period of the economic reform of China that became known as the "socialist market economy". Superseding the political ideologies of the Cultural Revolution, the reform led China towards a market economy and opened up the market for foreign investors. Nonetheless, despite the economic freedom, values and political ideas of the Chinese Communist Party (CCP) have had to be protected by "swatting flies" of other unwanted ideologies.[22]
The internet in China arrived in 1994,[23] as the inevitable consequence of and supporting tool for a "socialist market economy". Gradually, while Internet availability has been increasing, the Internet has become a common communication platform and tool for trading information.
The Chinese government's control over the Internet began in 1996 when Premier Li Peng signed State Council Order No. 195, issuing the "Interim Regulations on the Management of International Networking of Computer Information Networks". Article 6 of the Regulations states: "Computer information networks that directly connect to the international network must use the international entry and exit channels provided by the Ministry of Posts and Telecommunications’ national public telecommunications network. No unit or individual may establish or use other channels to connect to the international network on their own." This regulation was later widely used to punish "climbing over the firewall".[24]
The Ministry of Public Security took initial steps to control Internet use in 1997, when it issued comprehensive regulations governing its use. The key sections, Articles 4–6, are:
Individuals are prohibited from using the Internet to: harm national security; disclose state secrets; or injure the interests of the state or society. Users are prohibited from using the Internet to create, replicate, retrieve, or transmit information that incites resistance to the PRC Constitution, laws, or administrative regulations; promoting the overthrow of the government or socialist system; undermining national unification; distorting the truth, spreading rumors, or destroying social order; or providing sexually suggestive material or encouraging gambling, violence, or murder. Users are prohibited from engaging in activities that harm the security of computer information networks and from using networks or changing network resources without prior approval.[25]
In 1998, the Chinese Communist Party feared that the China Democracy Party (CDP) would breed a powerful new network that CCP elites might not be able to control.[26] The CDP was immediately banned, followed by arrests and imprisonment.[27] That same year, the GFW project was started. The first part of the project lasted eight years and was completed in 2006. The second part began in 2006 and ended in 2008. On 6 December 2002, 300 people in charge of the GFW project from 31 provinces and cities throughout China participated in a four-day inaugural "Comprehensive Exhibition on Chinese Information System".[28] At the exhibition, many western high-tech products, including Internet security, video monitoring and human face recognition were purchased. It is estimated that around 30,000–50,000 police were employed in this gigantic project.[29]

Fang Binxing is known for his substantial contribution to China's Internet censorship infrastructure, and has been dubbed "Father of China's Great Fire Wall".[30][31][32]
Remove ads
Origins of Chinese Internet law
Summarize
Perspective
China's view of the Internet is one of "Internet sovereignty": the notion that the Internet inside the country is part of the country's sovereignty and should be governed by the country.[12][33]
While the United States and several other western countries passed laws creating computer crimes beginning in the 1970s, China had no such legislation until 1997. That year, China's sole legislative body – the National People's Congress (NPC) – passed CL97, a law that deals with cyber crimes, which it divided into two broad categories: crimes that target computer networks, and crimes carried out over computer networks. Behavior illegal under the latter category includes, among many things, the dissemination of pornographic material, and the usurping of "state secrets."[34]
Some Chinese judges were critical of CL97, calling it ineffective and unenforceable. However, the NPC claimed that it intentionally left the law "flexible" so that it could be open to future interpretation and development. Given the gaps in the law, the central government of China relies heavily on its administrative body, the State Council, to determine what falls under the definitions, and their determinations are not required to go through the NPC legislative process. As a result, the Chinese Communist Party has ended up relying heavily on state regulation to carry out CL97.[35]
The latter definition of online activities punishable under CL97, or "crimes carried out over computer networks", is used as justification for the Great Firewall, and can be cited when the government blocks any ISP, gateway connections, or any access to anything on the internet. The definition also includes using the internet to distribute information considered "harmful to national security," and using the internet to distribute information considered "harmful to public order, social stability, and Chinese morality." The central government relies heavily on its State Council regulators to determine what specific online behavior and speech fall under these definitions.[citation needed]
The reasons behind the Internet censorship in China include:
- Social control: the Internet is a means for freedom of speech, and dissemination of campaigns could lead to protests against the government.
- Sensitive content: to control information about the government in China.
- Economic protectionism: China prefers the use of local companies that are regulated by Chinese regulations, since they have more power over them, e.g. Baidu over Google.[citation needed][36]
Remove ads
Campaigns and crackdowns
Summarize
Perspective
As part of the Great Firewall, beginning in 2003, China started the Golden Shield Project, a massive surveillance and censoring system, the hardware for which was provided by mostly U.S. companies, including Cisco Systems. The project was completed in 2006, and is now carried out in buildings with machines operated by civilians and supervised by China's national police force, the Public Security Bureau (PSB). The main operating procedures of the gatekeepers at the Golden Shield Project include monitoring domestic websites, email, and searching for politically sensitive language and calls to protest. When damaging content is found, local PSB officials can be dispatched to investigate or make arrests. However, by late 2007, the Golden Shield Project proved to operate sporadically at best, as users had long adapted to internet blocking by using proxy servers, among other strategies, to make communications and circumnavigate to blocked content.[37]
Internet cafés, an extremely popular way of getting online in developing countries and where fewer people can afford a personal computer, are regulated by the Chinese government and by local Chinese government officials. Minors (in China, those under the age of 18) are not allowed into Internet cafés, although this law is widely ignored, and when enforced, has spurred the creation of underground "Black Web Bars" visited by those underage. As of 2008, internet cafés were required to register every customer in a log when they used the internet there. These records may be confiscated by either local government officials or the PSB. To illustrate local regulation of internet cafés, in one instance, a government official in the town of Gedong lawfully banned internet cafés from operating in the town because he believed them to be harmful to minors, who frequented them to play online games (including those considered violent) and surf the internet. However, internet cafés in this town simply went underground, and most minors were not deterred from visiting them.[38]
In May 2015, China indefinitely blocked access to the Chinese-language Wikipedia.[39] In 2017, China discussed plans for its own version of Wikipedia.[40][41] As of May 2019, all language versions of Wikipedia have been blocked by the Chinese government.[42]
Remove ads
Blocking methods
Summarize
Perspective
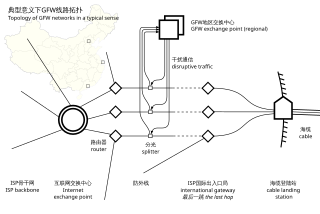
The Great Firewall is mainly deployed at three large internet exchanges in Beijing, Shanghai, and Guangzhou.[43][44]
Active filtering
One function of the Chinese firewall is to selectively prevent content from being accessed. It is mostly made of Cisco, Huawei, and Semptian hardware.[45][46] Not all sensitive content gets blocked; in 2007, scholar Jedidiah R. Crandall and others argued that the main purpose is not to block 100%, but rather to flag and to warn, in order to encourage self-censorship.[47] An illustrative but incomplete list of tactics includes:
Active probing
In addition to previously discussed techniques, the CAC is also using active probing in order to identify and block network services that would help escaping the firewall. Multiple services such as Tor or VPN providers reported receiving unsolicited TCP/IP connections shortly after legitimate use, for the purported purpose of network enumeration of services, in particular TLS/SSL and Tor services, with the aim of facilitating IP blocking. For example, shortly after a VPN request is issued by a legitimate Chinese VPN client and passes outbound though the Great Firewall to a hidden VPN IP, the Great Firewall may detect the activity and issue its own active probe to verify the nature of the previously unknown VPN IP and, if the probe confirms the IP is part of a blacklisted VPN, blacklist the IP.[74][75] This attack can be circumvented with the Obfs4 protocol, which relies on an out-of-band shared secret.[74][75]
Proxy distribution
The Great Firewall scrapes the IPs of Tor and VPN servers from the official distribution channels, and enumerates them.[76][77][78][79] The strategy to resist this attack is to limit the quantity of proxy IPs revealed to each user and making it very difficult for users to create more than one identity.[80][81][82] Academics have proposed solutions such as Salmon, a volunteer-based proxy network designed to combat censorship.[83][84][85][86] Dynamic IPs are quite effective to flush out from blacklists.
Remove ads
Goals, impact and resistance
Summarize
Perspective
Goal of the Firewall
Article 15 of a 20 September 2000 document from the Chinese State Council, posted by the Xinhua News Agency, lists 9 categories of information which should be censored, blocked, or filtered from access to the citizens using the internet within China:
- Opposing the basic principles as they are confirmed in the Constitution.
- Jeopardizing the security of the nation, divulging state secrets, subverting state power, or jeopardizing the integrity of the nation's unity
- Harming the honor or the interests of the nation
- Inciting hatred against peoples, racism against peoples, or disrupting the solidarity of peoples
- Disrupting national policies on religion, propagating evil cults and feudal superstitions
- Spreading rumors, disturbing social order or disrupting social stability
- Spreading obscenity, pornography, gambling, violence, murder, terror, or abetting the commission of a crime
- Insulting or defaming third parties, infringing on the legal rights and interests of third parties
- Containing any other content prohibited by law or administrative rules[87]
To filter this content, the Chinese government not only uses its own blocking methods, but also heavily relies on internet companies, such as ISPs, social media operators such as Weibo,[88] and others to actively censor their users.[89] This results in private companies censoring their own platform for filtered content, forcing Chinese internet users to use websites not hosted in China to access this information. Much of this information is related to sensitive topics.[90] The Great Firewall's goal is perceived by the Chinese Communist Party as helping to protect the Chinese population by preventing users from accessing these foreign websites which, in their opinion, host content which would be 'spiritual pollution', as well as information about these sensitive topics.[91] These topics include:
- Names of paramount leaders, such as Xi Jinping and Deng Xiaoping
- Political movements and protests
- Falun Gong and other spiritual groups
- The Tiananmen Square Massacre
- The Xinjiang internment camps
- Discussions of Tibetan Independence[92][93][94]
A 2020 study found that the Great Firewall blocks approximately 311,000 domains.[95][96]
Impact on people in China
The Cybersecurity Law behind the firewall is targeted at helping increase internet user privacy, increase protections on personal data, and making companies more responsible for monitoring bad actors, in hopes to make the Internet a safer place for Chinese citizens.[97] Despite this, there have been growing criticisms that the actions of the Chinese government have only hurt Chinese free speech, due to increased censorship, and lack of non-sanctioned sources of information, such as Wikipedia and many English news sources.[96] This has resulted in reports of some cases of legal persecution of those charged with spreading this information.[91]
The Chinese government itself does legally support free speech; article 35 of the Constitution of China states that "citizens of the People's Republic of China enjoy freedom of speech, of the press, of assembly, of association, of procession, and of demonstration."[98] In recent decades, many criticisms of the Chinese government found that some of these laws are often abused. A study by PEN America claimed that "Some of the government's most rights-abusive laws are aimed at criminalizing free speech that — in the eyes of the government — encourages subversion, separatism, or rejection of the State’s authority."[90]
Censorship of sensitive topics in China has also been easier for the government because of the firewall and its filtering. Because the monitoring of social media and chat apps in China presents a possibility of punishment for a user, the discussion of these topics is now limited to the thought of the Chinese Communist Party, or one's home and private spaces, reducing the chance for information about these topics to spread, reducing any threat of protest against the CCP.[99][100] According to Yaqiu Wang, a prominent human rights researcher, there was a time in China where the internet provided a method for Chinese citizens to learn about the sensitive topics the government had censored in the news, through access to international news reports and media coverage. She claims that, in the past 10 years, it has been increasingly difficult to access second opinions on events, meaning that students rarely have the opportunity to learn diverging viewpoints — only the "correct" thought of the CCP.[99]
Economic impacts
The Great Firewall has also allowed China to develop its own major internet services, such as Tencent, Alibaba, Baidu,[101][102] Renren, Youku, and Weibo.[103]: 8 China has its own version of many foreign web properties, for example: Bilibili and Tencent Video (YouTube), Weibo (Twitter), Moments[104] and Qzone (Facebook), WeChat (WhatsApp), Ctrip (Orbitz and others), and Zhihu[105] (Quora). With nearly one quarter of the global internet population (700 million users), the internet behind the GFW can be considered a "parallel universe" to the Internet that exists outside.[12]
Resistance
While the Great Firewall has had an impact on Chinese citizens' ability to use the internet to find information about sensitive topics about the Chinese Communist Party, it has not completely stopped them from doing so. The firewall itself has caused much frustration amongst both individuals and internationally operating companies in China, many of whom have turned to VPNs, speaking in codes,[106] and other methods to retain their access to the international internet.[107]
Remove ads
Circumvention
Summarize
Perspective
Methods for bypassing the firewall
Because the Great Firewall blocks destination IP addresses and domain names and inspects the data being sent or received, a basic censorship circumvention strategy is to use proxy nodes and encrypt the data. Bypassing the firewall is known as fānqiáng (翻墙, "climb over the wall"), and most circumvention tools combine these two mechanisms:[108]
- Proxy servers outside China can be used, although using just a simple open proxy (HTTP or SOCKS) without also using an encrypted tunnel (such as HTTPS) does little to circumvent the sophisticated censors.[108]
- Freegate, Ultrasurf, Psiphon, and Lantern are free programs designed and experienced with circumventing the China firewall using multiple open proxies.
- VPNs (virtual private networks) are one of the most popular tools used by Westerners for bypassing censorship technologies.[109] They use the same basic approaches, proxies, and encrypted channels used by other circumvention tools, but depend on a private host, a virtual host, or an account outside of China, rather than open, free proxies.[108]
- Tor partially can be used in China.[108][110] Since 2010, almost all bridges at TorProject.org are blocked through proxy distribution. Tor still functions in China using Snowflake,[111] independently published Obfs4 bridges and meek.[112][113][114][115]
- I2P or garlic routing is useful when properties similar to Tor's anonymity are needed. Due to I2P being much less popular than Tor, it has faced little to no blocking attempts.
In 2017, the Chinese government declared unauthorized VPN services illegal, requiring VPN providers to obtain state approval.[116] Although China restricts VPNs, they remain widely used by private individuals.[117]: 109 State-owned enterprises or state institutions also use VPNs for official work.[117]: 109 The Chinese government has authorized several official VPN providers.[117]: 109 Those who develop or sell their own VPNs potentially face years in prison.[117]: 109
Non-proxy circumvention strategies include:
- Using encrypted DNS may bypass blocking of a few sites including TorProject and all of GitHub, which may be used to obtain further circumvention.[118] In 2019 Firefox released an update to make it easy to enable DNS over HTTPS.[119] Despite DNS over encryption, the majority of services remain blocked by IP.[120]
- Ignoring TCP reset packets sent by the GFW. Distinguishing them by the TTL value (time to live), and not routing any further packets to sites that have triggered blocking behavior.[121]
Known blocked methods
- The OpenVPN protocol is detected and blocked. Connections not using symmetric keys or using "tls-auth" are blocked at handshake, and connections using the new "tls-crypt" option are detected and throttled (under 56 kbit/s) by the QoS filtering system.[citation needed]
- GRE tunnels and protocols that use GRE (e.g., PPTP) are blocked.[citation needed]
- TLS, the Great Firewall can identify the difference between HTTPS TLS and other implementations by inspecting the handshake parameters.[122][123][124][125]
Remove ads
Outside China
Summarize
Perspective
Off-target incidents
In 2010, a root name server run by Netnod in China started returning poisoned DNS results to global users, preventing users in Chile and the U.S. from accessing sites such as Facebook. The server was shut down to stop the poisoning.[126]
In 2014, two-thirds of China's DNS infrastructure began resolving unrelated domains to 65.49.2.178, an address owned by the US-based Dynamic Internet Technology, Inc., resulting in widespread internet outage in China. No damage to DIT services were reported despite what amounts to an accidental DDoS. While some sources attribute this incident to GFW's DNS poisoning,[127] others (mostly quoting Chinese sources) speculate this incident was somehow caused by DIT themselves.[128]
Exporting Great Firewall technology
Reporters Without Borders suspects that countries such as Cuba, Iran,[129] Vietnam, Zimbabwe, and Belarus have obtained surveillance technology from China, although the censorship in these countries is less stringent than in China.[130]
Since at least 2015, the Russian Roskomnadzor agency collaborates with Chinese Great Firewall security officials in implementing its data retention and filtering infrastructure.[131][132][133] During his visit to Beijing in June 2016, Vladimir Putin signed a joint communiqué with Xi Jinping on information space, followed by Russia's National Forum for Information Security in October hosted by Fang Binxing, the architect of the Chinese Great Firewall.[132]
Especially since the 2022 Russian invasion of Ukraine, in order to enforce the war censorship law, Russian authorities were making an internet surveillance system akin to Chinese Great Firewall.[134]
Opposition
Critics have argued that if other large countries begin following China's approach, the whole purpose of the creation of the Internet could be put in jeopardy. If like-minded countries are successful in imposing the same restrictions on their inhabitants and globalized online companies, then the free global exchange of information could cease to exist.[135]
The United States Trade Representative's (USTR) "National Trade Estimate Report" in 2016 referred the China's digital Great Firewall: "China's filtering of cross-border Internet traffic has posed a significant burden to foreign suppliers."[136] Claude Barfield, the American Enterprise Institute's expert of International trade, suggested that the U.S. government should bring a case against the Firewall, a huge trade barrier, in the World Trade Organization in January 2017.[137] Eight of the 24 more trafficked websites in China have been blocked by the Great Firewall. This has created a burden to foreign suppliers who rely on these websites to sell their products or services. The lobby's 2016 business climate survey showed 79 percent of its members reported a negative impact on business due to internet censorship.[138]
According to Stephen Rosen, the GFW is reflective of the Chinese government's fear of civil disobedience or rebellion among the Chinese population against the Chinese Communist Party's rule:
If you want to know what people are worried about look at what they spend their money on. If you’re afraid of burglars you buy a burglar alarm. What are the Chinese spending their money on? We’re told from Chinese figures they’re spending on the People's Armed Police, the internal security force is about as big as they’re spending on the regular military. This whole great firewall of China, this whole massive effort to control the internet, this effort to use modern information technology not to disseminate information, empowering individuals, but to make people think what you want them to think and to monitor their behavior so that you can isolate and suppress them. That’s because this is a regime which is fundamentally afraid of its own people. And it’s fundamentally hostile to them.[139]
Remove ads
See also
- List of websites blocked in mainland China
- Bamboo Curtain
- Censorship in China
- Censorship of Wikipedia by China
- Cypher
- Great Cannon — A distributed denial-of-service attack tool co-located with the Great Firewall.
- GreatFire — An organization monitoring and providing apps, 12 websites, code, tests and tools related to the Great Firewall
- Green Dam Youth Escort
- Great Wall of Sand
- International Freedom of Expression Exchange – monitors[140]
- Internet censorship circumvention
- Media of China
- Politics of China
- Splinternet
- Who Controls the Internet?
Remove ads
Notes
References
Further reading
External links
Wikiwand - on
Seamless Wikipedia browsing. On steroids.
Remove ads